 This past week, The Wall Street Journal published an article which reported on the fallout from the European Court of Justice’s 2014 ruling that Google is required to remove links in European search results for individuals whose reputations are harmed by them.
This past week, The Wall Street Journal published an article which reported on the fallout from the European Court of Justice’s 2014 ruling that Google is required to remove links in European search results for individuals whose reputations are harmed by them.
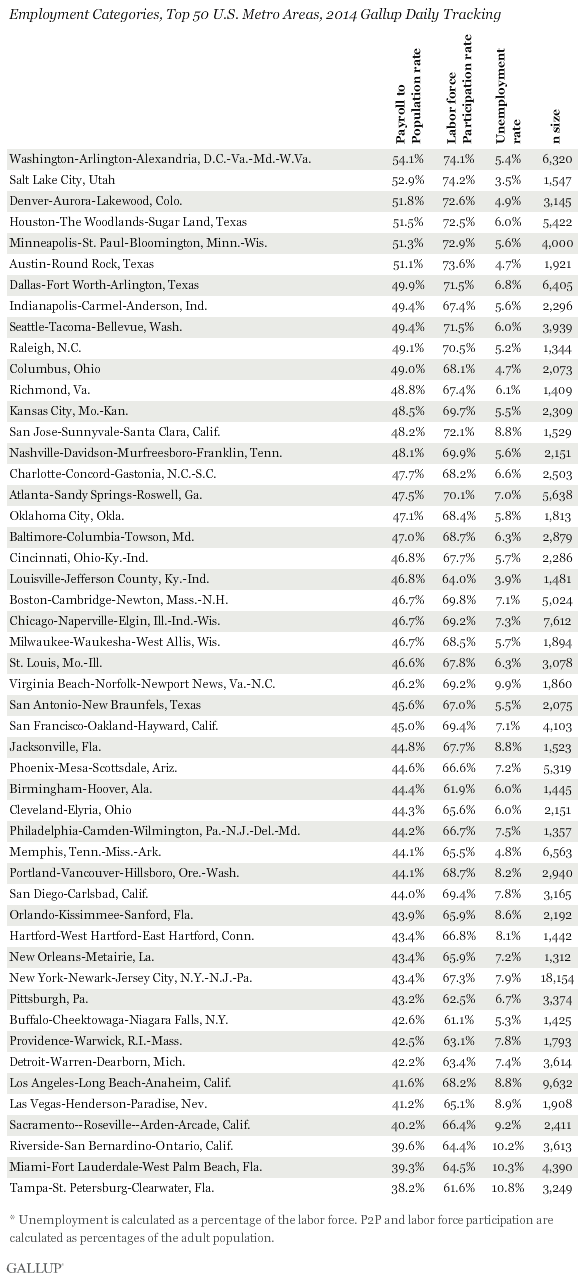
In practice, it’s turned out to be quite a conundrum. Since the ruling went into effect, Google has had to field requests to remove nearly 950,000 links from European search results.
Each request is deliberated on a case-by-case basis by a panel of specialists. Reportedly, Google has dozens of attorneys, paralegals and engineers assigned to the task, which is based at its European headquarters facilities in Dublin, Ireland.
So far, approximately one-third of the links in question have been removed while about half were deemed acceptable to continue displaying in search results. The remaining cases – the gnarliest ones – are still under review.
Unfortunately, the European Court of Justice hasn’t been very specific on the standards to apply when evaluating each request – other than to assert that search results should be removed that include links to information that is:
- Irrelevant
- Inadequate
- Excessive
- Harmful
- Outdated
Which, of course, could encompass practically anything. But the broader standard the Court has sought to uphold is “the right to be forgotten.”
Google hasn’t exactly been a willing participant in these mini-dramas. Peter Fleischer, Google’s global privacy counsel, contends that Google has been compelled “to play a role we never asked to play – and don’t want to play.”
Lisa Fleisher and Sam Schechner, the authors of the Wall Street Journal article, noted several examples of criteria that Google appears to be using when evaluating individual requests for removal.
More likely to be removed are search entries pertaining to crimes committed long ago and expunged from criminal records … nude or other revealing photos published without the permission of the subjects … and arrest records for petty infractions.
Less likely to be removed: stories about public figures.
As for the “group dynamics” involved in the decision-making, Fleischer reports that the committee’s votes are normally “a large majority in favor of one decision or the other.”
Looking ahead, as the experiment in parsing web search results to remove certain links while retaining others continues, it’s sure to have implications worldwide.
One reason is that, for now at least, Google has been removing search results only from European domains such as google.it or google.es, but not from the far-more-ubiquitous U.S.-based google.com – even when accessed from Europe.
This means that the “offending” search results can continue to be viewed, retrieved and opened easily.
That fact isn’t sitting well with EU privacy regulators. In fact, they’ve already issued an opinion contending that Google’s actions are insufficient, and they are seeking wider compliance. The potential price for not doing so is – you guessed it – legal action.
As time goes on, it will be interesting to see what ends up leeching into the American sphere when it comes to the ability of people to have erroneous or unflattering information about them that is currently so readily visible removed from view.
Clearly there are competing principals at work: freedom of information versus reputation protection.
 Court documents and similar documentation have always been public-access information, of course. But up until a few years ago, anyone interested in trolling for “dirt” on an individual or a company had to do costly, proactive searching through reams of paper-based documents.
Court documents and similar documentation have always been public-access information, of course. But up until a few years ago, anyone interested in trolling for “dirt” on an individual or a company had to do costly, proactive searching through reams of paper-based documents.
Not only was it a labor-intensive process that might or might not result in anything of substance, the source information itself was scattered among thousands of county seats all across America.
That alone was enough to guarantee that most documents were effectively far away from public view.
But in today’s everything-digitized world, court documents – many dating back decades – have been optically scanned and can now be keyword-searched within an ounce of your life.
 What used to take months and cost plenty can now be researched in a matter of minutes.
What used to take months and cost plenty can now be researched in a matter of minutes.
And beyond court or government documentation is the press, which can get things very wrong (or simply premature) when reporting on controversial or titillating news items.
It affects companies as well as individuals. I recall one such example in Baltimore from a number of years ago. The local business press reported on a lawsuit brought by a disgruntled creditor against another company. (I’m not naming the companies in question in deference to their reputations.)
The press reporting focused on the plaintiff’s petition to force the company into bankruptcy by virtue of the alleged “unpaid debt.” The fact that the substance of the suit was found wanting and the defendant firm cleared of wrongdoing made little difference when it came to the reputation of the company and its principals; the original news reports continue to have a life online, years later.
As the CEO the defendant company wrote to the publication involved,
“We now live in an age where digital documents take on a life of their own, and where it is no longer sufficient to consider whether someone might read a newspaper article on a given page on a given day. Now, with the press of a button articles are stored in massive servers and retrieved by anyone around the world, leaving innocent people branded forever by erroneous words and faulty assumptions.
It is your ethical responsibility to avoid causing undue harm to innocent parties by prematurely publishing information that others will negative construe and act upon. Waiting a little longer to clarify the facts and determine the truth is sensible public policy and only makes your paper’s articles more trustworthy and fair, thereby avoiding the journalistic equivalent of shouting ‘fire’ in a crowded theater.”
It seems to me that we’re just starting down a road with this issue, and we don’t really know where it’s going to end up.
Considering everything – the European Court of Justice, Google and the global nature of “search and destroy,” I’d be interested in hearing what readers think about the situation, the competing issues, and the ultimate destination.
 Time was, the online experience was blissfully free of annoying advertising. (Of course, that was back in the very early days of the Internet.)
Time was, the online experience was blissfully free of annoying advertising. (Of course, that was back in the very early days of the Internet.)